Cybercrime, Ransomware Tactics, Dark Web Intelligence
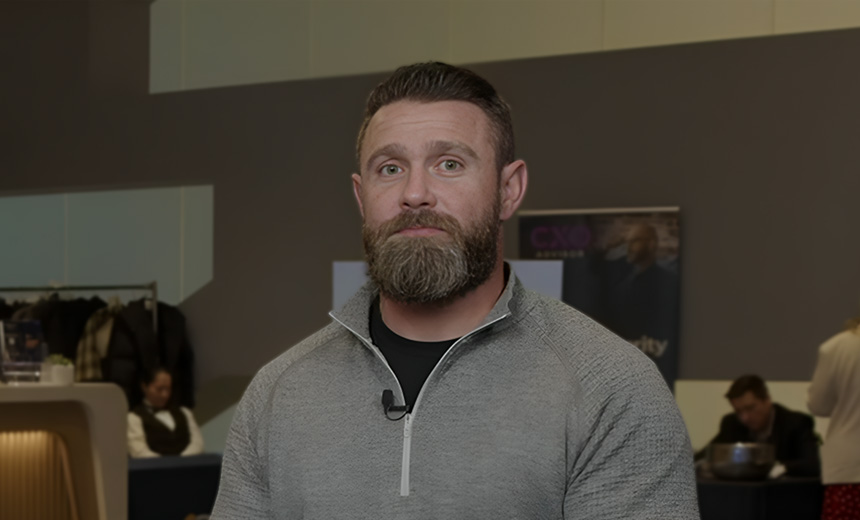
Insight from Ryan Cole at Searchlight Cyber on Combatting Decentralized Cyber Threats
Financial institutions remain a primary target for cybercriminals, including ransomware groups and initial access brokers who eagerly exploit lucrative networks. These actors have increasingly adopted decentralized ransomware-as-a-service models that allow them to operate with greater resilience. Ryan Cole, a product technical specialist at Searchlight Cyber, emphasizes that “if a centralized model gets taken down, it’s game over for that operation,” making decentralization a more sustainable approach.
The Franchise Model of Cybercrime
Cole likens the decentralized model of these cyber operations to a franchise system. He states, “If one group faces an attack, others can quickly step in and continue their activities.” This structure not only preserves the group’s operational capabilities but also complicates enforcement efforts against them. It highlights the sophisticated tactics these organizations employ to protect their ransomware strategies.
Exploiting Vulnerabilities with Anonymity
Initial access brokers utilize the anonymity provided by the dark web, foreign safe havens, and a variety of tools to amplify ransomware threats. They often target third-party vendors, which typically have weaker defenses. Cole advises, “If you want to outsmart them, you need to think like they do. Anticipate their moves and virtually attack your own systems before they can.” He emphasizes the critical nature of speed in identifying vulnerabilities—who acts first can often determine the outcome of a potential attack.
Key Discussion Points in Cybersecurity
In a recent video interview conducted by the Information Security Media Group at the Fraud and Financial Services Summit in New York, Cole elaborated on several vital topics in the realm of cybersecurity. These included:
- The significant role of the dark web in credential sales.
- How gaps in the supply chain heighten the risk of breaches.
- The benefits of simulating attacks on an organization’s infrastructure to uncover weak spots in security.
The Role of Dark Web Intelligence
With over a decade of experience in the field, Cole plays a pivotal role in Searchlight Cyber’s product team, showcasing the tactical advantages of dark web intelligence to potential clients. His expertise centers on guiding organizations in leveraging dark web data to bolster their threat intelligence and enhance investigations into cybercrime.